10 mins read

What Is a Sandbox Browser?
In the rapidly evolving landscape of artificial intelligence (AI) and autonomous agents, the concept of a sandbox browser has emerged as a foundational primitive for robust and secure web interaction. A sandbox browser is an isolated, containerized instance of the Chromium browser engine that separates all agent-driven web activities from the host system.
The core principle behind a sandbox browser is simple yet powerful: each web interaction is executed within a disposable container, ensuring that cookies, credentials, downloads, and any injected scripts are fully contained within that boundary and destroyed when the container exits. This stark contrast to the common practice of running headless Chromium directly on the host system, which can be dangerous for autonomous agents as it exposes the host to potential security risks and contamination.
By encapsulating the browser within a containerized environment, the sandbox browser approach provides a secure and controlled way for AI agents to navigate the web. This isolated layer acts as a barrier, preventing the accidental or malicious transfer of data, credentials, or malware from the web into the host system. The sandbox browser effectively quarantines the web interaction, ensuring that the agent's actions and their consequences remain confined within the disposable container.
The significance of the sandbox browser extends beyond just security; it also enables greater flexibility and scalability in AI agent infrastructure. By spinning up and tearing down browser instances on-demand, the sandbox browser allows for efficient resource management, enabling agents to quickly adapt to changing web environments and tasks without burdening the host system.
As the AI industry continues to evolve, the sandbox browser has solidified its place as a fundamental component of modern agent-driven web interaction. This isolated Chromium layer provides a secure and scalable foundation for a wide range of AI applications, from web scraping and data extraction to automated testing and content generation. In the coming years, the sandbox browser will undoubtedly play a crucial role in empowering the next generation of AI agents to navigate the ever-expanding web with confidence and safety.
Why AI Agents Need Isolated Browsers
In the rapidly evolving landscape of AI assistants, the need for a robust and secure browser environment has never been more crucial. As AI agents become increasingly powerful and integrated into our daily lives, the risks associated with granting them unfettered access to the open web have grown exponentially. The consequences of such access can be severe, with malicious actors exploiting vulnerabilities to compromise the agent's security and privacy, as well as the integrity of the data it processes.
One of the primary concerns is the potential for malicious web pages to inject scripts that can exfiltrate sensitive session tokens, enabling unauthorized access to user accounts and data. Furthermore, sophisticated prompt injection attacks can trick the agent into leaking confidential information, jeopardizing the privacy and security of the individuals and organizations relying on the AI's services. Even seemingly innocuous actions, such as accessing local files via the file:// protocol, can lead to unintended data leaks and breaches.
Equally worrisome is the risk of credential theft from the agent's own browser profile, where login credentials and other sensitive information may be stored. This can have far-reaching consequences, as the compromised credentials could be used to gain unauthorized access to critical systems and applications, potentially leading to data breaches, financial losses, and reputational damage.
Sandboxing is no longer an optional feature for production-ready AI agents; it has become a non-negotiable requirement. By isolating the browser environment from the core AI system, organizations can effectively mitigate these threats, ensuring that the agent's interactions with the web remain secure and contained. This approach not only protects the agent's integrity but also safeguards the sensitive data it processes, allowing for the secure deployment of AI-powered applications in mission-critical scenarios.
As we look to the future, the need for a robust and secure browser environment will only become more pressing. AI agents are poised to play an increasingly integral role in our lives, and it is our responsibility as developers and users to ensure that these powerful tools are deployed with the utmost care and consideration for security and privacy. The sandbox browser is a critical component in this endeavor, providing the isolated layer of protection that every AI agent stack needs to thrive in the digital landscape of 2026 and beyond.
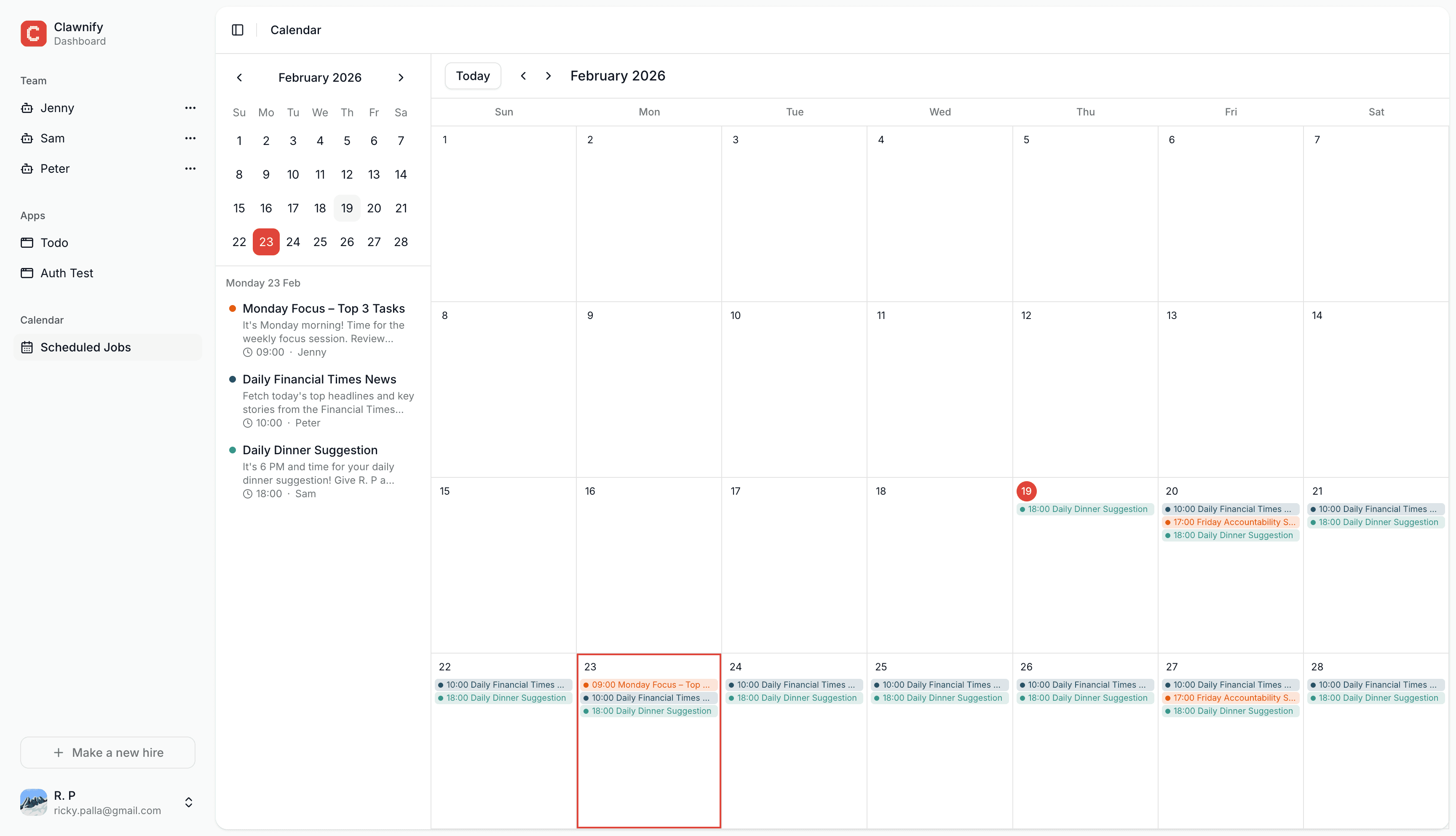
Run AI agents in a safe sandbox
Make your first hire with Clawnify
How a Sandbox Browser Works: Architecture Deep Dive
At the heart of a robust sandbox browser solution is a containerized Chromium instance, running in an isolated Docker environment with conservative security hardening. This self-contained, fully encapsulated browser runtime provides a secure, sandboxed layer for AI agents to interact with the web, shielded from the host system and other running processes.
The sandbox browser workflow begins with the agent communicating to the Docker container via the Chrome DevTools Protocol (CDP), a robust API that exposes Chromium's inner workings. The agent can then drive the browser, navigate to websites, extract data, and even execute JavaScript—all within the confines of the isolated runtime.
To enable visual observation of the sandbox in action, the solution integrates noVNC, a HTML5-based VNC client. This allows a human operator to watch the agent's activities in real-time through a password-protected, short-lived URL. The noVNC viewer acts as a secure window into the sandbox, providing valuable debugging and monitoring capabilities.
For enhanced security, the sandbox can be further hardened through CIDR-based IP allowlists, restricting network access to only approved domains and IP ranges. Workspace bind mounts also enable fine-grained control over file system access, with the ability to grant read-only, read-write, or no access to specific directories.
The flexibility of the sandbox browser approach extends to custom Docker image support. Users can bring their own Chromium-based browser images, tailored to their specific needs, ensuring a perfect fit for their AI agent stack. This level of configurability is crucial for enterprises operating in regulated industries or with unique security requirements.
By encapsulating the web browsing functionality within a secure, isolated sandbox, the sandbox browser empowers AI agents to safely and reliably interact with online resources, without the risk of compromising the host system or exposing sensitive data. This architectural approach is set to become a cornerstone of AI agent stacks in the years to come.
Key Features That Define a Production-Ready Sandbox Browser
As artificial intelligence and machine learning models become more advanced and prevalent, the need for a robust, reliable, and scalable sandbox browser environment has never been greater. When evaluating sandbox browser solutions for your AI agent stack in 2026, there are several key features that define a truly production-ready platform.
Zero-Config Auto-Start: The best sandbox browser solutions should require zero configuration to get up and running. With a simple API call or web interface, you should be able to instantly spin up a fully-functional, isolated sandbox browser environment, ready to execute your AI agent's tasks without any manual setup or intervention.
Disposable Container Lifecycle: Each sandbox session should run within a disposable container, ensuring complete isolation and preventing any cross-contamination between tasks. When the session is complete, the container should be automatically destroyed, leaving no trace and preparing the environment for the next AI agent to execute its workload.
Real-Time noVNC Observation: For debugging and monitoring purposes, the sandbox browser should provide a real-time noVNC (HTML5 VNC) interface, allowing you to observe the browser's activity as your AI agent interacts with web content, without the need for any additional software or plugins.
CIDR-Scoped CDP Access: The sandbox browser should offer secure, CIDR-scoped access to the Chrome DevTools Protocol (CDP), enabling your AI agents to programmatically interact with the browser and extract valuable insights and data from the web pages they visit.
Configurable Workspace Access Modes: Depending on your use case, the sandbox browser should support various workspace access modes, such as read-only, read-write, and disposable, allowing you to control the level of interaction your AI agents have with the simulated browser environment.
Custom Docker Image Support: For advanced users and specialized use cases, the sandbox browser should allow the integration of custom Docker images, enabling you to tailor the browser environment to your specific needs, whether it's pre-installing custom extensions or running on a specific version of Chromium.
Token-Protected Short-Lived Access URLs: To ensure the security and integrity of your sandbox browser sessions, the platform should provide short-lived, token-protected access URLs that automatically expire after a predetermined time, preventing unauthorized access or prolonged usage of the isolated environment.
When compared to managed cloud-hosted services like Firecrawl Browser Sandbox, a truly production-ready sandbox browser should offer all of these features and more, providing a reliable, scalable, and secure foundation for your AI agent stack in the years to come.
Getting Started: Sandbox Browsers in Practice with OpenClaw
As we've explored, the need for a robust sandbox browser is critical for any AI agent stack in 2026 and beyond. Fortunately, the OpenClaw platform provides a turnkey solution for integrating this crucial capability into your system. Let's dive into how OpenClaw makes it easy to leverage the power of sandboxed Chromium browsing.
At the heart of OpenClaw's sandbox browser functionality is a self-hostable, Docker-backed system that automatically provisions a sandboxed Chromium container when you invoke the browser tool. This containerized approach ensures complete isolation of your browsing activities, shielding your core systems from any potential malicious code or unexpected behavior.
One of the standout features of OpenClaw's sandbox browser is the noVNC interface. This web-based remote desktop allows you to interact with the sandboxed browser seamlessly, as if you were using a local instance. The intuitive interface makes it easy to navigate the web, execute tasks, and view rendered content, all while maintaining the critical isolation provided by the sandbox.
But OpenClaw goes beyond just the noVNC interface. The platform also offers a powerful CLI tool, the openclaw sandbox command, which allows you to manage and interact with your sandbox environments programmatically. This makes it easy to integrate the sandbox browser functionality into your AI agent workflows, automating tasks and ensuring consistent, reliable access to the isolated browsing environment.
OpenClaw supports three backend options for its sandbox browser, giving you the flexibility to choose the solution that best fits your needs:
Docker (recommended): The preferred option, the Docker backend provisions a sandboxed Chromium container on-demand, ensuring complete isolation and ease of management.
SSH: For scenarios where Docker may not be available, the SSH backend allows you to leverage a remote SSH-accessible host to run the sandbox browser.
OpenShell: This backend is designed for maximum portability, running the sandbox browser directly on the local machine without any external dependencies.
With OpenClaw, you can seamlessly incorporate the power of sandbox browsers into your AI agent stack, empowering your systems to safely and reliably interact with the web, without compromising the integrity of your core infrastructure. Try it out today and see how this cutting-edge technology can transform your AI agent capabilities.