10 mins read

At the heart of every OpenClaw deployment is the gateway -- a Node.js WebSocket server that, by default, listens on port 18789. It is the central nervous system of your AI agent: every message from WhatsApp, Telegram, Discord, or iMessage flows through it; every tool call, shell command, and file read is orchestrated by it; and every API key, conversation log, and connected credential lives within its reach. Without the gateway, your AI agent is inert. With unrestricted access to it, an attacker controls everything your agent can do.
That framing is what makes the gateway such an attractive target. Unlike a typical web server that serves static content, the OpenClaw gateway is an authenticated execution environment. A compromised gateway does not just leak data -- it lets an attacker issue commands to your AI, exfiltrate your API keys, read your memory files, trigger shell execution on the host, and pivot to any connected service your agent has access to. In the wrong hands, it is essentially a remote administration tool with AI superpowers.
The gateway's local-first design was intended to minimize this risk. Running on loopback (127.0.0.1), it should never be reachable from the internet. But the defaults are permissive, and developer convenience has a habit of expanding the attack surface. A quick firewall exception to reach the gateway from a second device, a Docker publish flag exposing port 18789 externally, or an nginx misconfiguration that proxies the WebSocket without authentication -- any of these common shortcuts can silently transform a private local gateway into a publicly reachable target.
Default port: 18789 (TCP, WebSocket)
Default bind: loopback -- but easily overridden by misconfiguration
Attack value: Full agent control, credential access, shell execution on host
Who is at risk: Anyone exposing the gateway to a network interface without token auth
Understanding what the gateway does -- and what an attacker gains by owning it -- is the essential foundation for the hardening steps that follow. The good news is that the attack surface is well-understood and almost entirely addressable through configuration, not code.
In February 2026, two vulnerabilities in rapid succession put OpenClaw gateway security on the front page of security research. Together they revealed not just a pair of bugs, but a systemic exposure problem affecting tens of thousands of real deployments.
ClawJacked (Patched in v2026.2.13)
Discovered by Oasis Security, the ClawJacked attack required zero user interaction. The attack flow was elegant and brutal: a malicious website opens a WebSocket connection to localhost:18789. Browsers permit this because CORS restrictions do not apply to localhost connections. The site then brute-forces the gateway password at high speed -- because localhost connections also bypass rate limiting. Once authenticated, the attacker auto-registers as a trusted device. No approval prompt. No notification. Full access: agent control, config dumps, shell execution, credential extraction, connected device enumeration.
CVE-2026-25253 (Patched in v2026.2.21)
The second vulnerability followed closely. Malicious JavaScript could steal the authentication token directly from the gateway WebSocket handshake, then use it to disable sandboxing and execute dangerous shell commands without the confirmation prompts OpenClaw normally requires for high-risk operations. This elevated the threat further: even token-authenticated gateways were vulnerable to token exfiltration if the token was transmitted insecurely during connection setup.
Vulnerability | Method | Impact | Patched In |
|---|---|---|---|
ClawJacked | WebSocket brute-force via malicious site | Full agent takeover, shell access | v2026.2.13 |
CVE-2026-25253 | Token exfiltration via WebSocket handshake | Sandbox bypass, unapproved command execution | v2026.2.21 |
The Scale Problem
CrowdStrike internet-wide scan at the time of disclosure found 42,000+ publicly reachable OpenClaw gateway instances, of which 93.4% were running vulnerable versions. Both patches shipped within 24-48 hours of disclosure. The patches were fast. The adoption was not. Self-hosted software only updates when the operator decides to update -- and most operators do not monitor security advisories for every tool they run. This gap between patch availability and patch adoption is the structural problem that no CVE fix can solve on its own.
Start using OpenClaw in an isolated computer
Hire your first (AI) employee
Here is the uncomfortable truth that security post-mortems often gloss over: both ClawJacked and CVE-2026-25253 required a misconfigured gateway to be exploitable in the first place. A gateway correctly bound to loopback, protected by a strong token, with strict file permissions, and accessed only via SSH tunnel would have been immune to both attacks even before the patches shipped. The vulnerability was real -- but the widespread exploitation was enabled by configuration choices, not by the software itself.
This matters because patching alone does not fix misconfiguration. A fully updated gateway running on 0.0.0.0 with no authentication token is still a wide-open target. And based on the CrowdStrike data, a large fraction of the 42,000+ exposed instances are still misconfigured in exactly this way today.
The Three Endemic Misconfigurations
Binding to 0.0.0.0 instead of 127.0.0.1: This is the single most dangerous misconfiguration. Binding to all interfaces makes the gateway reachable from any network the host is connected to. Docker port publish flag silently creates this exposure even when the compose file looks safe. Always verify with
netstat -tulpn | grep 18789and confirm the output shows127.0.0.1:18789, not0.0.0.0:18789.Missing or weak authentication: The default OpenClaw config does not enforce token auth on new installations. Many users skip this step during onboarding. Without a strong token, ClawJacked-style brute-force attacks and unauthenticated WebSocket connections are trivially easy.
World-readable config and token files: The gateway config at
~/.openclaw/openclaw.jsoncontains API keys, channel tokens, and the gateway auth secret. If this file has default permissions (644), any process running as another user on the same machine can read it. On shared hosting environments, this is a critical exposure.
Misconfiguration | Risk Level | Fix |
|---|---|---|
Binding to 0.0.0.0 | Critical |
|
No auth token | Critical |
|
Config file readable by others | High |
|
Patching is necessary. It is not sufficient. A hardening checklist applied once -- and verified periodically -- is what actually closes the gap.
Run through these six steps in order. Each one closes a specific, documented attack vector. All commands are for Ubuntu/Debian; adjust paths as needed for macOS or other distributions.
Step 1 -- Bind to Loopback Only
In your ~/.openclaw/openclaw.json, set: gateway.bind: loopback and gateway.port: 18789. Verify with netstat -tulpn | grep 18789 -- output must show 127.0.0.1:18789, never 0.0.0.0.
Step 2 -- Enforce Token Authentication
Set the auth mode to token and store the token in an environment variable, never hardcoded: gateway.auth.mode: token and gateway.auth.token: ${OPENCLAW_GATEWAY_TOKEN}. Generate a strong token with openclaw doctor --generate-gateway-token.
Step 3 -- Lock Down File Permissions
chmod 600 ~/.openclaw/openclaw.json and chmod 700 ~/.openclaw/. Verify with ls -la ~/.openclaw/openclaw.json -- should show -rw-------.
Step 4 -- Tunnel Remote Access Over SSH or VPN
Never publish port 18789 to the internet. For remote access, use SSH forwarding: ssh -L 18789:127.0.0.1:18789 user@your-server. Or use Tailscale to create a private mesh network. Both approaches keep the gateway invisible to the public internet while remaining accessible to authorized operators.
Step 5 -- Firewall Port 18789 at the Network Boundary
Run sudo ufw deny 18789. For Docker deployments, ensure the compose file does NOT publish the port externally -- avoid ports: - 18789:18789 unless you have a specific authenticated reverse proxy in front of it.
Step 6 -- Pin Versions and Automate Update Checks
Subscribe to OpenClaw GitHub release feed. Add a weekly check of your running version (openclaw --version) against the latest release tag. Run openclaw security audit --deep after any configuration change. If it returns no critical findings, your posture is solid.
Step | Command/Setting | Closes |
|---|---|---|
Loopback bind |
| Remote network exposure |
Token auth |
| ClawJacked brute-force |
File permissions |
| Credential file reads |
SSH/VPN tunnel | SSH -L or Tailscale | Insecure remote access |
Firewall |
| Public port exposure |
Version pinning | GitHub release feed | Patch adoption lag |
Hardening your gateway once is necessary. Keeping it hardened as OpenClaw evolves, as your infrastructure changes, and as new vulnerabilities are inevitably discovered requires a repeatable process. Here is how to build one that does not consume significant time.
Track OpenClaw Releases
Subscribe to GitHub release notifications for openclaw/openclaw. Every release includes a changelog that explicitly flags security fixes -- look for entries tagged security, fix(security), or CVE. The ClawJacked and CVE-2026-25253 patches shipped within 48 hours of disclosure; being subscribed meant knowing about them the same day. Being unsubscribed meant joining the 93.4% statistic.
For Docker-based deployments, a monthly docker compose pull && docker compose up -d combined with a version check is a minimal but meaningful update cadence.
Use the Built-In Security Audit
OpenClaw includes a built-in audit command designed exactly for this purpose. Run it periodically and after any configuration change:
openclaw security audit --deep
A clean run should confirm: loopback bind active, token auth enforced, config permissions 600, no publicly reachable endpoints. If any check fails, the output tells you exactly which setting to correct.
Verify You Are Not Still Exposed
Check whether your gateway is internet-reachable from outside your network using a simple test from a remote server or Shodan. If it connects, your firewall is misconfigured -- fix it immediately.
Action | Frequency | Command |
|---|---|---|
Check for new releases | Weekly | GitHub release feed |
Pull and update containers | Monthly |
|
Run security audit | Monthly |
|
Verify bind address | After network changes |
|
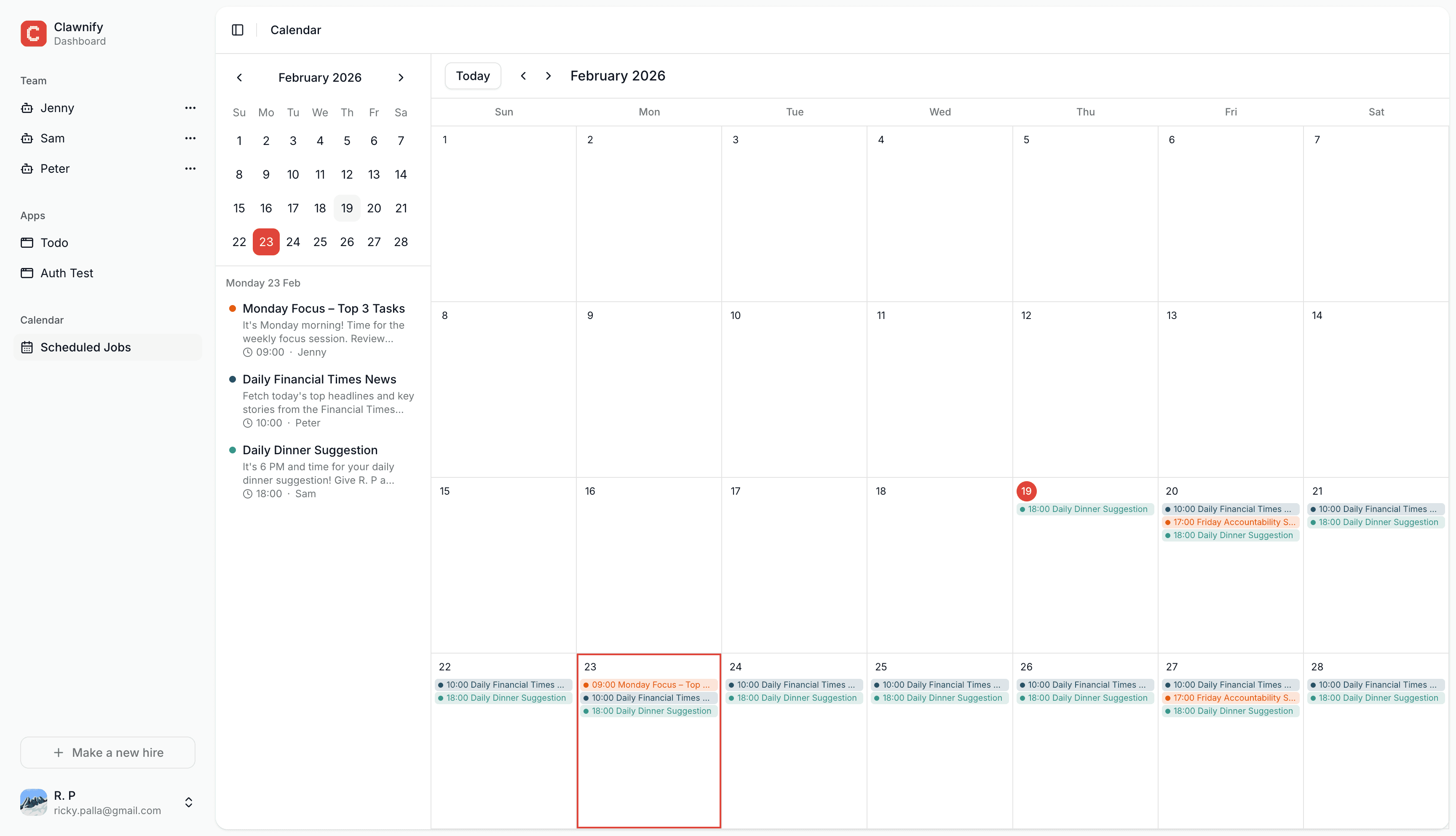
If managing this cadence feels like overhead, it is a reasonable signal to consider a managed platform. Clawnify.com applies security patches automatically the moment they ship, enforces hardened gateway defaults by design, and removes the operator from the update loop entirely. For teams where agent uptime and data security are business-critical, that is not a convenience feature -- it is a meaningful risk reduction.
Start now: run openclaw security audit --deep and confirm your version is current before you close this tab.